PASSWORD RECOVERY
Elcomsoft Distributed Password Recovery
High-Performance Distributed Password Recovery
Break complex passwords, recover strong encryption keys and unlock documents in a production environment. Elcomsoft Distributed Password Recovery is a high-end solution for forensic and government agencies, data recovery and password recovery services and corporate users with multiple networked workstations connected over a LAN or the Internet. Featuring unique acceleration technologies and providing linear scalability with no overhead, Elcomsoft Distributed Password Recovery offers the fastest password recovery by a huge margin, and is the most technologically advanced password recovery product currently available.
Features and Benefits
- Hardware acceleration (patented) reduces password recovery time by a factor of 250
- Support for the latest NVIDIA Blackwell architecture
- Support for Intel built-in graphic cores, dedicated NVIDIA CUDA and AMD Radeon HD graphics cards as hardware accelerators
- Heterogeneous acceleration allows mixing GPU brands and models
- Resource management allows administrators to easily manage and allocate the available computational resources across multiple jobs
- Portable tools for live system analysis allow extracting hashes from a range of encrypted containers and password managers
- Linear scalability with zero overhead supporting up to 10,000 workstations
- On-demand deployment of Amazon EC2 and Microsoft Azure cloud instances
- Supports encrypted volumes created by all common crypto containers including BitLocker, FileVault 2 (including APFS volumes), LUKS and LUKS2, TrueCrypt, VeraCrypt, PGP and Jetico BestCrypt.
- Recovers passwords to popular backup tools by Acronis, Macrium, and Veeam
- Custom dictionaries automatically distributed across active agents
- Allows up to 64 CPUs or CPU cores and up to 32 GPUs per processing node
- Broad compatibility recovers document and system passwords to various file formats
- Brute-force attack with flexible masks
- Dictionary attack with mutations and custom mutation rules
- Distributed password recovery over LAN, Internet or both
- Console management for flexible control from any networked PC
- Plug-in architecture allows for additional file formats
- Flexible load balancing with scheduling
- Minimum bandwidth utilization
- All network communications between password recovery clients and the server are securely encrypted
- Flexible queue control allows easy job management
- Storing all passwords that have been discovered, forming a separate/internal dictionary (password cache)
- Remote client deployment and deinstallation
- Agents and server can run as system services without an active user session
- Logs CPU time and resource utilization, password recovery jobs and user activities
- Industry certified: Microsoft Gold Certified Partner, Intel Software Partner, NVIDIA Developer Support
Hardware Acceleration
Elcomsoft Distributed Password Recovery employs a revolutionary, patented technology to accelerate password recovery when a compatible NVIDIA or AMD graphics card is present in addition to the CPU-only mode. Hardware acceleration utilizes GPU cores of NVIDIA GeForce RTX boards, AMD GPUs, as well as GPU cores built into Intel CPUs including Intel HD Graphics, UHD Graphics and Intel Iris.
The acceleration technology offloads parts of computational-heavy processing onto the fast and highly scalable processors featured in the latest graphic accelerators, achieving unprecedented recovery speeds exceeding those available to CPU-only users by significant margin.
ElcomSoft pioneered asynchronous hardware acceleration. Heterogeneous acceleration allows using multiple video cards of different makes and models, effectively utilizing existing hardware and squeezing the last bit of performance out of every supported component.
Resource Management
The resource management capability is a game-changer for busy environments. The feature allows administrators to easily manage and distribute the available computational resources across multiple jobs. The administrative server enables users to tap into a pool of available resources by requesting a certain number of recovery agents for a given password recovery job. The reserved recovery agents will be allocated to that one job, allowing multiple tasks to run separately at the same time.
In essence, resource management simplifies the process of managing and utilizing the available computational resources by several jobs, ultimately leading to improved efficiency and scalability. Here's how it works:
Strict Protection of Sensitive Information
The included Elcomsoft Hash Extractor tool allows extracting encryption metadata from a wide range of file formats. By using encryption metadata to set up attacks, you are automatically excluding the possibility of potentially sensitive information such as raw or encrypted data falling into the wrong hands as none is included in the extracted hash files.
Elcomsoft Hash Extractor enables to set up attacks on a tiny hash file instead of the original, potentially large file or document. Since no raw or encrypted data is included in encryption metadata, the hash files produced with Elcomsoft Hash Extractor offer significantly higher level of privacy, allowing remote and cloud processing without the risk of a content leak.
The optional portable version of this tool allows for better portability and flexibility, offering significantly easier extraction of password and encryption hashes from live systems.
Elcomsoft Hash Extractor supports all major Microsoft Office, Open Document, Apple iWork, and Adobe Acrobat formats, as well as LastPass and 1Password password managers and LM/NTLM/DCC hashes. The full list of supported formats is available below.
| Application | File extension/Source |
|---|---|
| 1Password | .js, .sqlite, .plist, .db, .xml |
| LastPass | .log, .sqlite, .xml |
| Dashlane | .dash, .aes, .log |
| KeePass | .key, .keyx |
| Microsoft Office | .doc, .dot, .xls, .xla, .xlw, .ppt, .pps .pps, .pot, .mny, .mbf, .one, .docx, .docm, .xlsx, .xlsm, .xlsb, .pptx, .pptm, .mpp, .accdb, .pages, .numbers, .key |
| Open Document | .odt, .ott, .odg, .otg, .odp, .otp, .ods, .ots, .odf, sxw, .stw, .sxd, .std, .sxi, .sti, .sxc, .stc, .sxm |
| Hancom Office | .hwp, .cell |
| Adobe Acrobat | |
| 7ZIP | .7z, .7z001, .exe |
| ZIP | .zip, .zipx, .exe, .sfx |
| RAR | .rar, .sfx, .exe |
| IZArc | .ize |
| Acronis True Image | .tib, .tibx |
| Veeam | .vbm, .vstore |
| Macrium Reflect | .mrimg, .mrbak |
| Windows Users (LM/NTLM hashes) | SAM, SYSTEM |
| Windows Users (DCC hashes) | SECURITY, SYSTEM |
Broad Compatibility
Elcomsoft Distributed Password Recovery supports a variety of applications and file formats, allowing password recovery from Office documents, Adobe PDF files, PGP disks and archives, personal security certificates and exchange keys, MD5 hashes, Windows and UNIX login passwords.
| Application family | Applications | Extensions | Type of recovery | Password types | Hardware Acceleration |
|---|---|---|---|---|---|
| ZIP archives | PKZip, WinZip | .ZIP, .EXE, .SFX | password | - | NVIDIA, AMD, Intel |
| ZIP archives | WinZip (AES) | .ZIPX. .EXE, .SFX | password | - | NVIDIA, AMD, Intel |
| Bitcoin Wallet | Bitcoin Core | wallet.dat | password | - | NVIDIA, AMD, Intel |
| 7zip archives | 7Zip | .7z, .7z.001, .EXE | password | - | NVIDIA, AMD, Intel |
| RAR archives | RAR/WinRAR 3/4/5 | .RAR | password | - | NVIDIA, AMD, Intel |
| Microsoft Office 2007, 2010 | Word, Excel, Access, PowerPoint, OneNote, Project | .DOCX, .XLSX, .ACCDB, .PPTX, .ONE, .MSPX | password | opening | NVIDIA, AMD, INTEL |
| Microsoft Office 2013, 2016, 2019 | Word, Excel, Access, PowerPoint, OneNote | .DOCX, .XLSX, .ACCDB, .PPTX, .ONE, .MSPX | password | opening | NVIDIA, AMD, INTEL |
| Microsoft Office XP/2003 | Word, Excel, PowerPoint | .DOC, .XLS, .PPT | password | opening | - |
| Microsoft Office 97/2000 | Word, Excel | .DOC, .XLS | password | opening | - |
| Microsoft Office 97/2000 | Word, Excel | .DOC, .XLS | key, guaranteed decryption | opening | - |
| Microsoft SQL Server | Microsoft SQL Server, Microsoft SQl Server Compact | .MDF, .SDF | password | - | NVIDIA, AMD, INTEL |
| OpenDocument | word processing | .ODT, .OTT, .SXW, .STW | password | - | NVIDIA, AMD, INTEL |
| OpenDocument | spreadsheets | .ODS, .OTS, .SXC, .STC | password | - | NVIDIA, AMD, INTEL |
| OpenDocument | presentations | .ODP, .OTP, .SXI, .STI | password | - | NVIDIA, AMD, INTEL |
| OpenDocument | graphics/drawing | .ODG, .OTG, .SXD, .STD | password | - | NVIDIA, AMD, INTEL |
| OpenDocument | formulae, mathematical equations | .ODF, .SXM | password | - | NVIDIA, AMD, INTEL |
| MyOffice | MyOffice Text, MyOffice Spreadsheet | .DOCX, .XLSX, .ODT, .ODTX | password | opening | NVIDIA, AMD, INTEL |
| Microsoft Money | Microsoft Money | .MNY | password | - | - |
| Intuit Quicken | Intuit Quicken | .QDF | password | - | NVIDIA, AMD, INTEL |
| Hangul/Hancom Office | Hanword | .HWP | password | - | - |
| Hangul/Hancom Office | Hancell | .CELL | password | - | NVIDIA, AMD, INTEL |
| Hangul/Hancom Office | Hancom Show | .SHOW | password | - | NVIDIA, AMD, INTEL |
| PGP | PGP zip archives | .PGP | password | - | NVIDIA |
| PGP | PGP secret key rings | .SKR | password | - | NVIDIA |
| PGP | PGP disk (volume encryption) | .PGD | password | - | NVIDIA |
| PGP | PGP self-decrypting archives | .EXE | password | - | - |
| PGP | PGP whole disk encryption | - | password | - | NVIDIA |
| Certificates | Personal Information Exchange certificates - PKCS #12 | .PFX, .P12 | password | - | NVIDIA, AMD, INTEL |
| VPN | Internet Key Exchange (IKE) passwords | - | password | - | NVIDIA, AMD, INTEL |
| TrueCrypt, VeraCrypt | TrueCrypt and VeraCrypt full disk encryption | - | password | - | NVIDIA |
| TrueCrypt, VeraCrypt | TrueCrypt and VeraCrypt encrypted containers | - | password | - | NVIDIA |
| BestCrypt | BestCrypt containers and volumes | - | password | - | - |
| BitLocker | BitLocker and BitLocker To Go disk encryption | - | password | - | NVIDIA, AMD |
| FileVault 2 | HFS/HFS+ and APFS full-disk encryption | - | password | - | NVIDIA, AMD |
| LUKS | LUKS disks and containers | - | password | NVIDIA | |
| LUKS2 | LUKS2 disks and containers | - | password | NVIDIA, AMD, INTEL | |
| Hashes | MD5 hashes | - | password | NVIDIA | |
| Hashes | Salted MD5 hashes | - | password | NVIDIA | |
| Hashes | SHA-1 | - | password | NVIDIA, AMD, INTEL | |
| Hashes | SHA-256 | - | password | NVIDIA, AMD, INTEL | |
| Hashes | SHA-512 | - | password | NVIDIA, AMD, INTEL | |
| Adobe Acrobat PDF X/XI/DC | PDF with 256-bit encryption | password | user and owner | - | |
| Adobe Acrobat PDF 9.x | PDF with 256-bit encryption | password | user and owner | NVIDIA, AMD | |
| Adobe Acrobat PDF 5-8 | PDF with 128-bit encryption | password | user and owner | NVIDIA, AMD | |
| Adobe Acrobat PDF | PDF with 40-bit encryption | password | user and owner | - | |
| Adobe Acrobat PDF | PDF with 40-bit encryption | key, guaranteed decryption | user | - | |
| System Passwords | Microsoft Windows | - | password | LM NTLM NTLMv1 NTLMv2 | NVIDIA |
| System Passwords | Microsoft Windows | - | password | SYSKEY | - |
| System Passwords | Microsoft Windows | - | password | DCC (Domain Cached Credentials) | NVIDIA, AMD, INTEL |
| System Passwords | UNIX | - | password | user | - |
| System Passwords | Mac OS X | login.keychain | password | keychain | NVIDIA, AMD, INTEL |
| System Passwords | Mac OS X | - | password | user | NVIDIA |
| System Passwords | Mac OS X | DMG | password | DMG image | NVIDIA |
| Password managers | KeePass | .KDBX, .KBD, .PWD | password | master | NVIDIA, AMD, INTEL |
| Password managers | KeePass (RDBX4) | .KBDX | password | master | - |
| Password managers | 1Password | Windows / macOS / Android / iOS; backups on Dropbox and iCloud Drive | password | master | NVIDIA, AMD, INTEL |
| Password managers | LastPass | Windows, macOS and Linux browser plug-ins, Android app | password | master | NVIDIA, AMD, INTEL |
| Password managers | Dashlane | Windows, macOS | password | master | NVIDIA, AMD, INTEL |
| Password managers | Bitwarden | Windows local account, Chromium-based Browser Extensions, Firefox Browser Extensions | password | master | NVIDIA, AMD, INTEL |
| Password managers | Dropbox Passwords | Edge Browser Extensions, Chrome Extensions, Firefox Browser Extensions | password | master | - |
| Password managers | Enpass | Windows | password | master | NVIDIA, AMD, INTEL |
| Password managers | Kaspersky | Windows | password | master | NVIDIA, AMD, INTEL |
| Password managers | Keeper | Windows | password | master | NVIDIA, AMD, INTEL |
| Password managers | Roboform | Windows | password | master | NVIDIA, AMD, INTEL |
| Password managers | Sticky Password | Windows | password | master | NVIDIA, AMD, INTEL |
| Password managers | Zoho Vault | Windows | password | master | NVIDIA, AMD, INTEL |
| System Passwords | Wireless networks | - | password | WPA and WPA2 | NVIDIA, AMD, INTEL, AVX2 |
| Lotus | Lotus Notes (RC2) | .ID | password | - | - |
| Lotus | Lotus Notes (AES) | .ID | password | - | NVIDIA, AMD, INTEL |
| Lotus | Lotus Notes | admindata.xml | password | - | - |
| Lotus | HCL Domino R12 | password | - | - | |
| Ritlabs | TheBat! | masterkey.dat | password | master | - |
| Ritlabs | TheBat! | .TBK | password | backup | - |
| Mozilla | Mozilla, FireFox, Thunderbird | - | password | master | - |
| iPhone/iPod/iPad backup | iTunes | - | password | - | NVIDIA, AMD (except iOS 10.0), INTEL |
| Apple iWork '09 | Pages, Numbers, Keynote | .pages, .numbers, .key | password | opening | NVIDIA, AMD, INTEL |
| Apple iWork 2013/2014 | Pages, Numbers, Keynote | .pages, .numbers, .key | password | opening | NVIDIA, AMD, INTEL |
| Tally Vault | Tally ERP 9 | .500, .900, .1800 | password | opening | - |
| Windows Easy Transfer | Windows Easy Transfer | .mig | password | - | |
| Parallels | Parallels virtual machines | config.pvs | password | - | |
| VirtualBox | VirtualBox virtual machines | .vbox | password | NVIDIA, AMD | |
| VMware | VMware virtual machines | .vmx | password | NVIDIA, AMD | |
| Acronis | Acronis True Image, Acronis Cyber Protect Home Office | .tib | password | backup | - |
| Acronis | Acronis True Image, Acronis Cyber Protect Home Office | .tibx | password | backup | NVIDIA, AMD, INTEL |
| Macrium | Macrium Reflect 8 | .mrimg, .mrbak | password | backup | NVIDIA, AMD, INTEL |
| Veeam | Veeam Backup & Replication | password | backup | NVIDIA, AMD, INTEL | |
| FileMaker | FileMaker Pro 10 - 19 | password | - | ||
| Bitcoin | Electrum Bitcoin Wallet | ? | ? | ? | NVIDIA, AMD, INTEL |
| Encrypted Archive | IZArc | .ize | ? | ? | NVIDIA, AMD, INTEL |
Important note: hardware acceleration (for specific file formats and algorithms only, see the above chart for details) works properly only on Windows Server 2003/2008/2012 and Windows 7/8/8.1/10; specific versions of NVIDIA/AMD drivers are required; some other restrictions apply (e.g. for some file formats, it is implemented for brute-force attack only, while dictionary attack only works on the CPU, regardless the settings).
Distributed Recovery with Linear Scalability and Cloud Computing
Unlike competition, Elcomsoft Distributed Password Recovery is not ‘virtually’ or ‘practically’ linear in scalability. By doubling the number of PCs working on a password, you cut the time required to recover a password by half.
By only transferring the bare minimum of information over the network, Elcomsoft Distributed Password Recovery allows for massively parallel operation, and scales linearly to as many as 10,000 workstations with no scalability overhead.
Elcomsoft Distributed Password Recovery enables distributed work over the LAN, Internet, or both. Minimum bandwidth requirements ensure no scalability overhead even for the slowest connections.
The convenient management console allows controlling Elcomsoft Distributed Password Recovery from any networked PC.
Users can quickly deliver additional computing power on demand by utilizing Amazon’s GPU-accelerating EC2 Compute Units and Microsoft Azure instances. Depending on performance requirements and budget constraints, Amazon EC2 or Microsoft Azure instances can quickly scale to speed up the job, and can be scaled back when not in use. Elcomsoft Distributed Password Recovery running in an Amazon cloud is a perfect solution when additional computational power is needed without the need to invest into building permanent infrastructure in-house.
With Elcomsoft Distributed Password Recovery supporting cloud compute instances, users can get as much speed as they need the moment they need. Support for additional cloud services is coming soon.
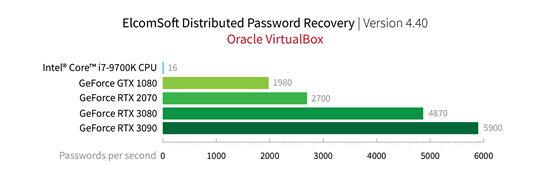
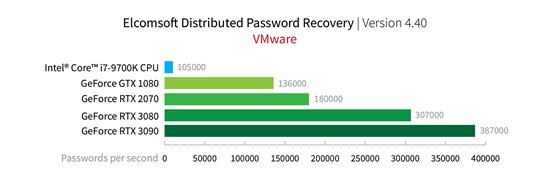
Access Evidence Stored in Encrypted Virtual Machines
The use of virtual machines is on the rise, enabling criminals cover their activities under a virtual umbrella. While storing massive amounts of evidence, an encrypted virtual machine can greatly reduce the risks of an accidental leak of incriminating evidence. Elcomsoft Distributed Password Recovery helps investigators gain access to all of that evidence by breaking the original encryption password.
Three of the most popular virtual machines are supported: VMware, Parallels, and VirtualBox. The tool can attack and recover the original VM encryption passwords, helping investigators to gain access stored in encrypted images.
How GPU Acceleration Works
Using brute force attack to recover passwords, it is possible, though time-consuming, to recover passwords from popular applications with the power of the computer’s main CPU. However, the computational power of a general purpose CPU is no longer sufficient to break into many types of data protected with modern encryption methods. Manufacturers utilize tens of thousands of iterations to intentionally slow down the recovery, making the job effectively impossible for all but the simplest passwords.
Elcomsoft Distributed Password Recovery utilizes dedicated high-performance cores found in today's video cards such as those manufactured by NVIDIA and AMD to offload parts of computational-intensive calculations onto the highly scalable video cards. Featuring several hundred GPU cores, a single video card can deliver the speed far exceeding the metrics of a high-end CPU. Elcomsoft Distributed Password Recovery uses thoroughly optimized algorithms, reaching recovery rates that are up to 250 times faster compared to CPU-only benchmarks.
Today's PC motherboards support multiple video cards. Thanks to ElcomSoft's proprietary heterogeneous computing, Elcomsoft Distributed Password Recovery supports a mix of up to 32 video cards even if they are of different makes and models, allowing for even faster password recovery applications for a modest increase in hardware costs. The tool allows mixing NVIDIA and AMD boards of different generations in a single PC.
For more details, see GPU Acceleration Frequently Asked Questions.
Benchmarks
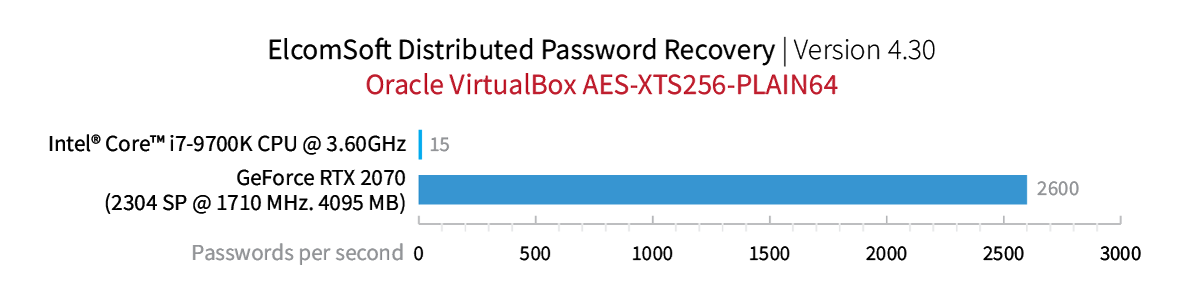
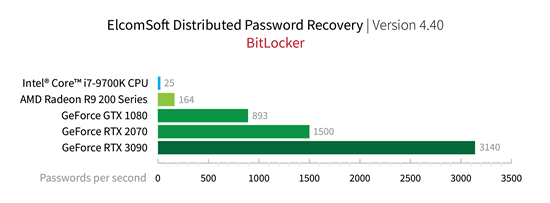
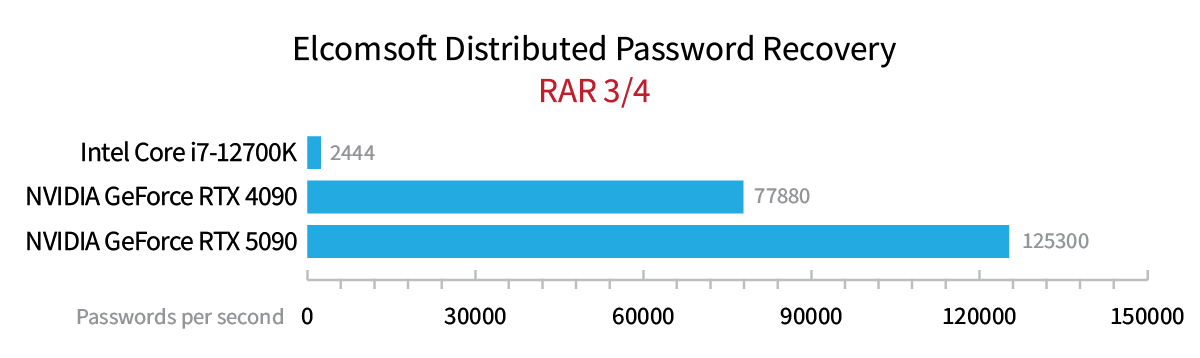
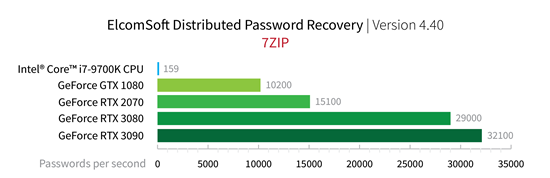
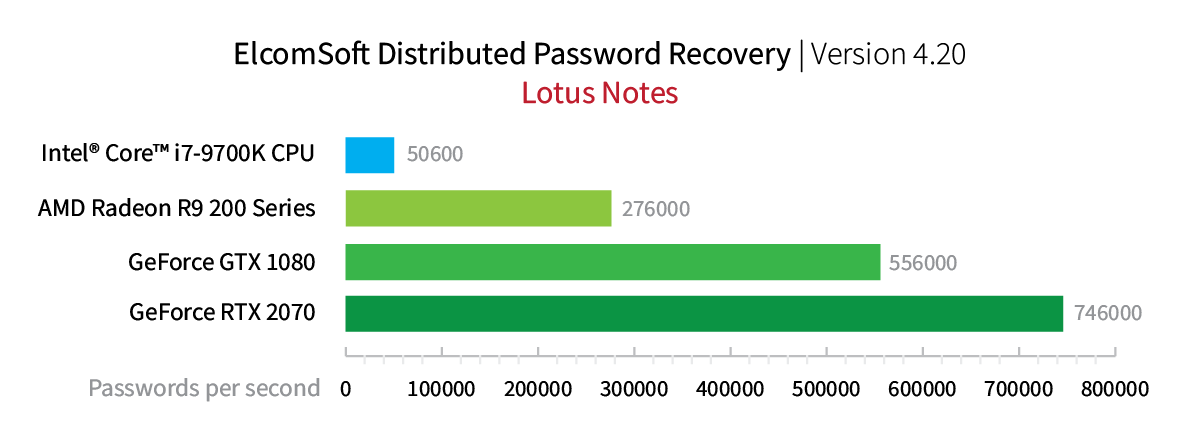
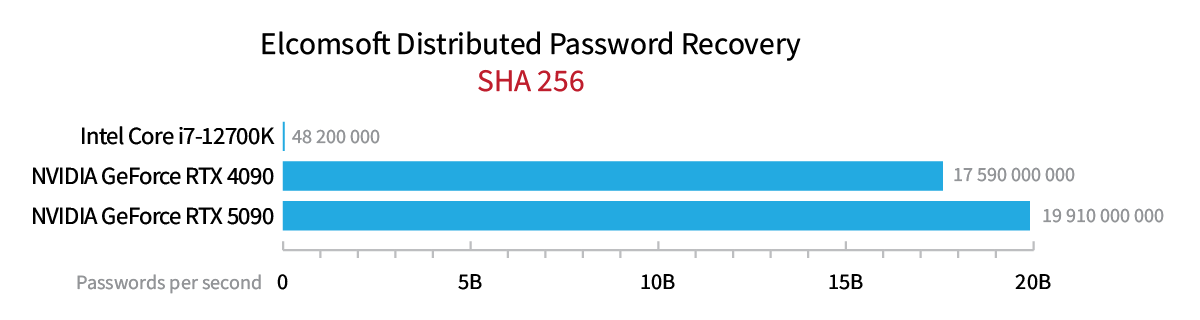
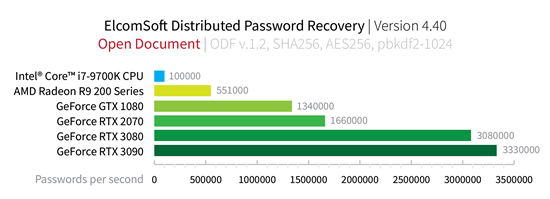
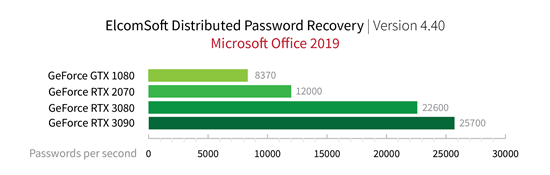
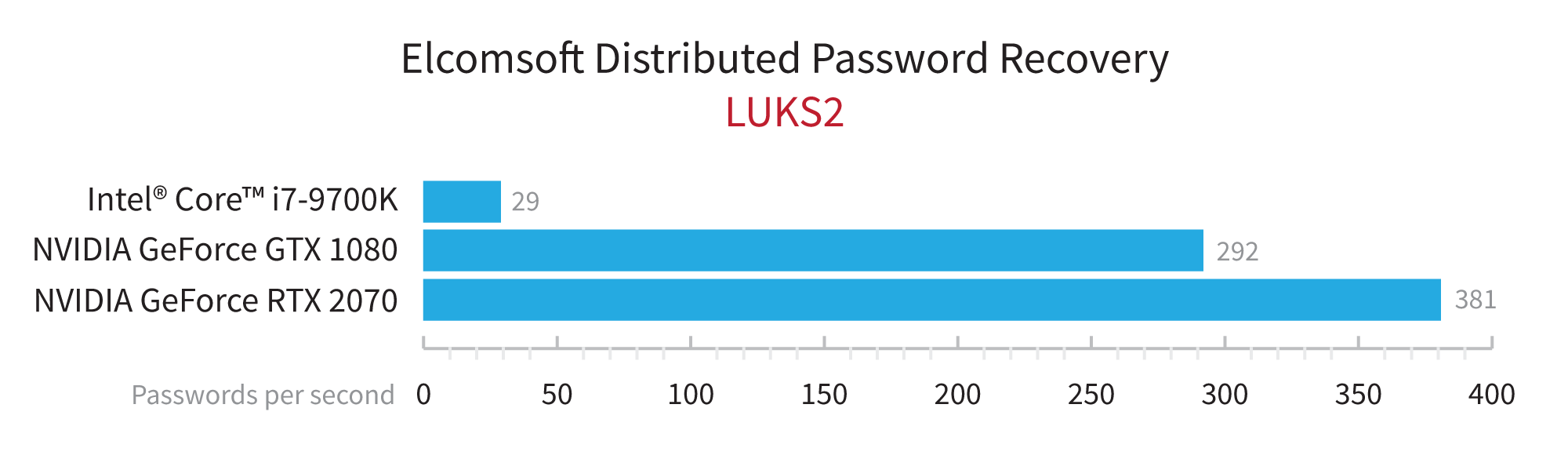
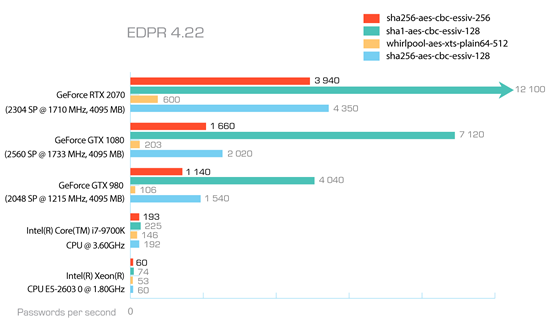
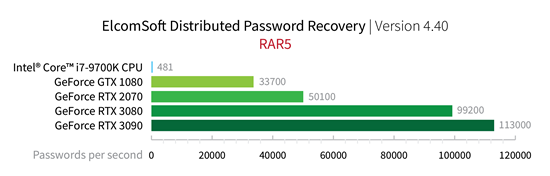
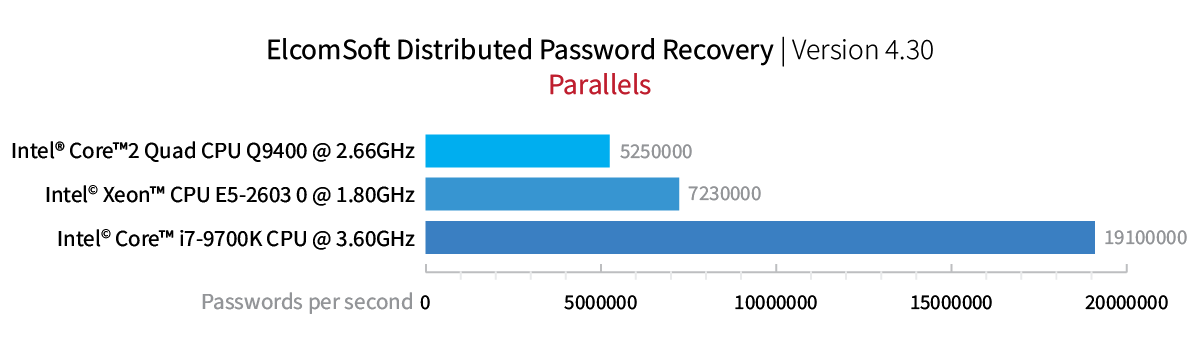
.png)
Wide Range of Formats Supported
Elcomsoft Distributed Password Recovery supports a variety of applications and file formats, allowing password recovery from Office documents, Adobe PDF files, PGP disks and archives, personal security certificates and exchange keys, MD5 hashes, Windows and UNIX login passwords and much more.
Archives
- ZIP (PKZip, WinZip) archives, conventional encryption
- ZIP (PKZip, WinZip) archives, AES encryption (GPU accelerated)
- RAR (WinRAR) archives (GPU accelerated)
- 7Zip archives (GPU accelerated)
Microsoft Office Documents
- Microsoft Office 2007: Word, Excel, Access, PowerPoint, Project (.DOCX, .XLSX, .ACCDB, .PPTX, .MSPX) file opening password recovery (GPU accelerated)
- Microsoft Office 2010: Word, Excel, Access, PowerPoint, OneNote (.DOCX, .XLSX, .ACCDB, .PPTX, .ONE) file opening password recovery (GPU accelerated)
- Microsoft Office 2013, 2016, 2019: Word, Excel, Access, PowerPoint, OneNote (.DOCX, .XLSX, .ACCDB, .PPTX, .ONE) file opening password recovery (GPU accelerated)
- Microsoft Word/Excel/PowerPoint XP/2003 (.DOC, .XLS, .PPT) (password recovery - "open" password only)
- Microsoft Word/Excel 97/2000 (.DOC, .XLS) (password recovery - "open" password only)
- Microsoft Word/Excel 97/2000 (.DOC, .XLS) (guaranteed decryption)
- Microsoft Money (password recovery)
- Microsoft OneNote (password recovery)
MyOffice (GPU accelerated)
- word processing (text) documents: .DOCX, .ODT, .OTT, .SXW, .STW
- spreadsheets: .XLSX, .ODS, .OTS, .SXC, .STC
OpenDocument (OpenOffice, StarOffice etc) (GPU accelerated)
- word processing (text) documents: .ODT, .OTT, .SXW, .STW
- spreadsheets: .ODS, .OTS, .SXC, .STC
- presentations: .ODP, .OTP, .SXI, .STI
- graphics/drawing: .ODG, .OTG, .SXD, .STD
- formulae, mathematical equations: .ODF, .SXM
(for full list of supported applications, see http://en.wikipedia.org/wiki/OpenDocument_software)
Apple iWork (GPU accelerated)
- Pages (.pages)
- Numbers (.numbers)
- KeyNote (.key)
Hangul/Hancom Office (Hanword, Hancell)
- Hanword 2010
- Hanword 2014
- Hancell 2010 (GPU accelerated)
- Hancell 2014 (GPU accelerated)
- Hancom Office Neo 2016 (GPU accelerated)
- Hancom Show
Disk encryption and Open-Key Passwords
- PGP zip archives (.PGP) (password recovery)
- PGP secret key rings (.SKR) (passphrase recovery) (GPU accelerated)
- PGP disks with conventional encryption (.PGD) (password recovery) (GPU accelerated)
- PGP self-decrypting archives (.EXE) (password recovery)
- PGP whole disk encryption (password recovery) (GPU accelerated)
- Personal Information Exchange certificates - PKCS #12 (.PFX, .P12) (password recovery) (GPU accelerated)
- IKE (Internet Key Exchange) dump (password recovery) (GPU accelerated)
- TrueCrypt and VeraCrypt (full disk encryption and encrypted containers) (GPU accelerated)
- LUKS and LUKS2 disks and containers (GPU accelerated)
- FileVault 2 (GPU accelerated) on both HFS/HFS+ and APFS volumes
- BitLocker and BitLocker To Go (GPU accelerated)
- BestCrypt 9 containers
Adobe Acrobat PDF
- Adobe Acrobat PDF with 256-bit encryption ("user" and "owner" password recovery) (GPU accelerated)
- Adobe Acrobat PDF with 128-bit encryption ("user" and "owner" password recovery)
- Adobe Acrobat PDF with 40-bit encryption ("user" and "owner" password recovery)
- Adobe Acrobat PDF with 40-bit encryption (guaranteed decryption)
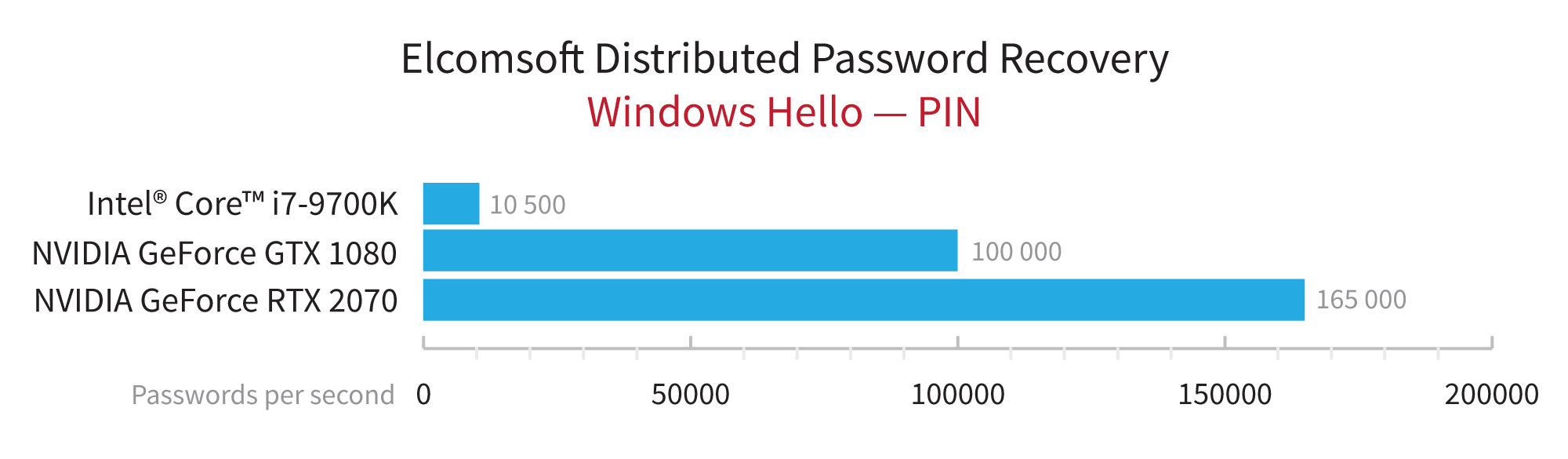
System Passwords
- Windows 11/10/8.1/8/7/Vista/XP/2000 (32 bit and 64 bit; all editions) Windows Server 2019/2016/2008/2003 logon passwords (LM/NTLM) (password recovery); Windows Hello PIN codes (non-TPM systems) (GPU accelerated)
- Windows SYSKEY startup passwords (password recovery)
- Windows DCC (Domain Cached Credentials) passwords (password recovery) (GPU accelerated)
- UNIX users’ passwords (password audit/recovery)
- Mac OS X account passwords (GPU accelerated)
Virtual Machines
- Parallels (fast CPU recovery), VirtualBox and VMware (GPU accelerated)
Backups
- Acronis True Image, Acronis Cyber Protect Home Office (.TIB, .TIBX)(password recovery) (GPU accelerated)
- Macrium Reflect 8 (.MRIMG, .MRBAK)(password recovery) (GPU accelerated)
- Veeam Backup & Replication (password recovery) (GPU accelerated)
Other Passwords and Hashes
- Intuit Quicken (.QDF) (password recovery)
- Lotus Notes ID files (password recovery) (GPU accelerated)
- MD5 hashes (plaintext recovery) (GPU accelerated)
- Salted MD5 hashes (plaintext recovery) (GPU accelerated)
- SHA-1/SHA-256/SHA-512 hashes (plaintext recovery) (GPU accelerated)
- WPA and WPA2 passwords (GPU accelerated)
- Mac OS X keychain password (GPU accelerated)
- TheBat! master passwords (masterkey.dat) and passwords to backups (*.tbk)
- Mozilla/FireFox/Thunderbird master passwords (password recovery)
- Microsoft SQL Server (.MDF) (password recovery) (GPU accelerated)
- Microsoft SQL Server Compact (.SDF) (password recovery) (GPU accelerated)
- iPhone/iPod/iPad backups (password recovery) (GPU accelerated)
- FileMaker databases
- Apple Disk Image (.DMG) passwords
- Password Managers: KeePass, LastPass, 1Password, Dashlane master password, Bitwarden, Dropbox Passwords, Enpass, Kaspersky, Keeper, Roboform, Sticky Password, and Zoho Vault
- Bitcoin Wallet passwords including Bitcoin Core, Classic, XT and Unlimited
- Tally ERP 9 Vault passwords
- Easy Transfer (.mig)
How to Order
Elcomsoft Distributed Password Recovery is licensed based on the number of instances (agents). We accept all major credit cards, checks, bank transfers and purchase orders. Sales taxes may be added to your order according to your jurisdiction. Credit card orders are processed immediately. Electronic licenses are generally available instantly after the credit card charge is approved. On rare occasions where we must manually verify your order, the license will be available in 48 hours or less.
